Exploited anew in Attacks on Government and Organizations
A zero-day vulnerability in FortiOS SSL-VPN that Fortinet addressed last month was exploited by unknown actors in attacks targeting the government and other large organizations. The attacks entailed the exploitation of CVE-2022-42475, a heap-based buffer overflow flaw that could enable an unauthenticated remote attacker to execute arbitrary code via specifically crafted requests.
The infection chain analyzed by the company shows that the end goal was to deploy a generic Linux implant modified for FortiOS that’s equipped to compromise Fortinet’s intrusion prevention system (IPS) software and establish connections with a remote server to download additional malware and execute commands.
The attackers were heavily focused on maintaining persistence and evading detection by using the vulnerability to install malware that patches FortiOS logging processes so that specific log entries could be removed, or to even kill the logging processes if necessary
Fortinet said it was unable to recover the payloads used in the subsequent stages of the attacks. It did not disclose when the intrusions took place.
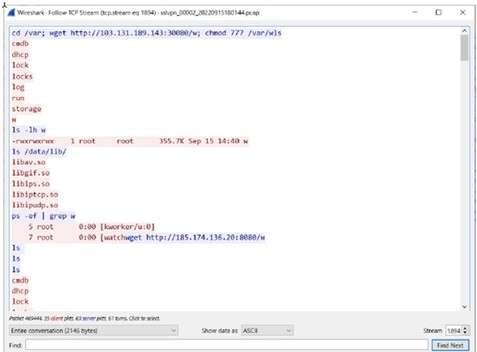
In addition, the modus operandi reveals the use of obfuscation to thwart analysis as well as “advanced capabilities” to manipulate FortiOS logging and terminate logging processes to remain undetected.
“It searches for log files, which are logs of events in FortiOS,” the researchers said. “After decompressing them in memory, it searches for a string the attacker specifies, deletes it, and reconstructs the logs.”
The network security company also noted that the exploit requires a “deep understanding of FortiOS and the underlying hardware” and that the threat actor possesses skills to reverse engineer different parts of FortiOS.
Since such type of attacks persist and have evolved, it is advised that there should be no postponing in updated to patched FortiOS versions and follow the instructions provided in our previous release.
References: