Can MDR solve the cybersecurity crisis? The short answer: Every generation has its take on how to do security. And each one thinks it has found the solution in new technology.
In the 1990s, the LAN firewall rose to prominence, followed by refinements in the form of unified threat management (UTM) and next-generation firewalls (NGFW) that put even more traffic inspection barriers in the way of malware communication.
All the while, at the user level, new layers of authentication were added, with sandboxing, DevSecOps development, threat intelligence and AI automation, and zero trust architectures arriving not far behind.
This has left corporate cybersecurity in a strange limbo. The technology looked promising, and yet as attackers move to exploit novel weaknesses and oversights, high-profile cyberattacks have not only continued to happen but worsened.
Attackers are no longer hopeful opportunists and have become industrial in their ambition. The response by enterprises has been to employ the same industrial techniques and automation as the attackers. But security at this scale becomes so complex, expensive, and skill-consuming, it has encouraged the industry to turn to security-as-a-service to make protection affordable and manageable.
MDR and MTTD
Managed threat detection and response (MDR) is at the front line of this new generation of security services: but can MDR turn the tide?
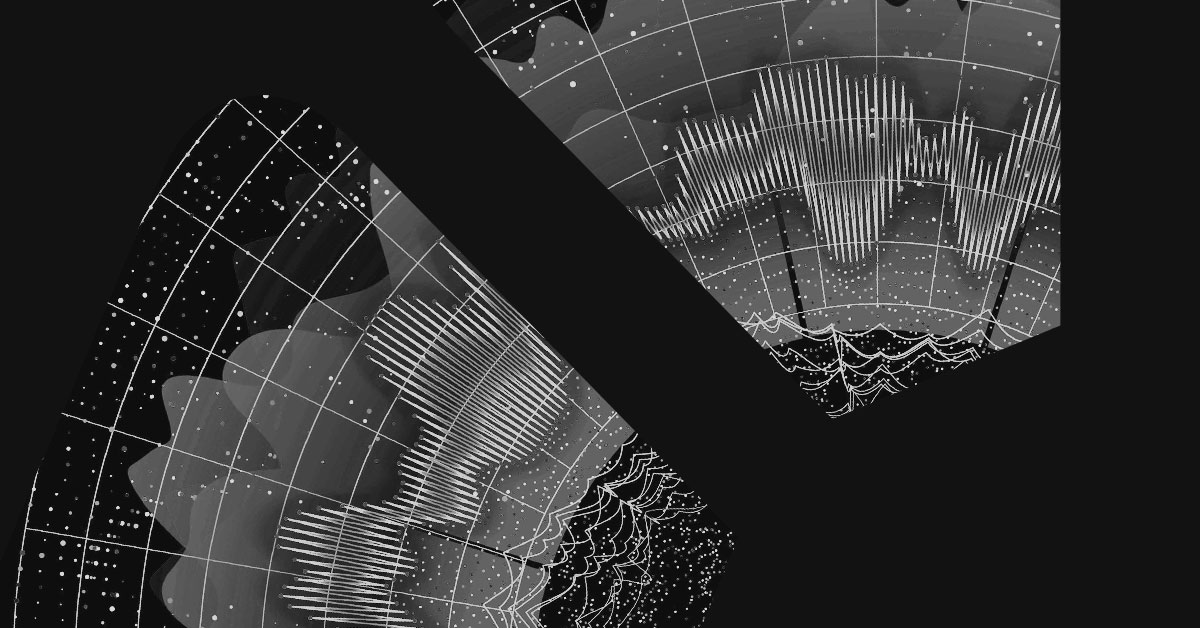
Cybersecurity defence is like a series of layers, with a failure of one layer making an organisation more vulnerable in every other. If endpoint security fails, that immediately gives the network layer a detection headache, which involves understanding alerts from several types of security sensors. In parallel, the same endpoint failure can quickly perpetuate the cloud applications that devices or end users access. At this point, the detection challenge becomes a multi-firewall WAN challenge for the Security Operations Centre (SoC) team.
Inevitably, endpoints become infected, which means that the measure of successful containment is how fast teams can notice and remediate. In MDR terms, we define infection as an incident that matters more how quickly it is detected than the detection itself. This is measured using the performance indicator Mean Time To Detect (MTTD).
MTTD is a powerful concept because it can be applied to any security system where response times matter, including MDR and patching and even DevOps remediation. Undoubtedly, what counts as good performance has shortened dramatically in recent years from weeks to days and hours. In the case of ransomware attacks, this is arguably now minutes and seconds.
The first MTTD upgrade MDR offers is that it’s a 24×7 service. That means there shouldn’t be any blind spots such as evenings, weekends, or holidays for attackers to target. That puts defenders back in the game. Not only for detection but also for the next piece of the puzzle: response measured as Mean Time To Respond (MTTR). The weapon of choice for MDR services here is automation because it is only by using such routines that MTTD can be turned into MTTR quickly enough.
MDR and in-house teams
At some point, every MDR service will need to assess more complex detections using experts. We cannot automate everything. Indeed, for larger customers, the response might require in-house teams to assess threats themselves using detections made by the MDR. These services can speed detection and response, but the efficient response depends on nuanced business decisions.
The most significant advantage of the MDR concept is that it takes the burden off in-house IT and SoC teams which now can do their intended job managing an organisation’s users, applications, and infrastructure. In theory, false positives should reduce while detection in terms of speed and accuracy should improve.
No need to buy in skills and investment in technology changes from CapEx to OpEx. This doesn’t necessarily save money upfront. However, it should reduce an organisation’s need to take bets on new technologies every few years.
Does MDR stop the technology treadmill?
MDR is not without its risks. Because it is a service, what is happening inside the service is not always clear from the customer side. Not all MDR services are the same. For example:
- What tools do we use as part of the service?
- Do these improve on the in-house tools?
- Does the MDR provider offer sector-specific services?
- Does the customer gain access to telemetry for deeper forensics? If so, in what form?
- How much response does the package include?
Conclusion
In the initial question, if MDR can solve the cybersecurity crisis, the longer answer is that using an MDR service presents organisations in a new and more manageable form. The problem of sizing and investing in security systems reduces. However, effectiveness is always something organisations must answer for themselves.